Industry Standard Policies and Tools
Documents
ALTA Outgoing Wire Preparation Checklist
Use this checklist as a best practice for verifying outgoing wire information.
Word Doc | PDF
ALTA Rapid Response Plan for Wire Fraud Incidents
Use this tool to customize your action plan when a wire fraud attempt occurs.
Word Doc | PDF
How to Complete an IC3 Report
Watch the video to learn how simple it is to assist law enforcement in gathering information.
ALTA Cybersecurity Incident Response Plan: Use this tool to help your team to establish and maintain secure systems and be prepared to act quickly if an incident occurs. Leverage these resources to implement Step 1: Preparation:
- ALTA Cyber System Overview: Use this narrative to improve your understanding of a Cyber System Inventory, why it is important to Cybersecurity efforts, and how to create and maintain your company's inventory.
- ALTA Cyber System Inventory Workbook: Use this model workbook to create and customize your company's inventory.
- ALTA Business Impact Analysis: Use this guide to examine your software applications, determine which resources are critical to your operation, and discover when to add resources to minimize the business impact of downtime.
Resources for Your Clients and Consumers
ALTA Wire Fraud Tips
(consumer video)
Protect Your Money from Wire Fraud Schemes
(consumer video)
ALTA Wire Fraud Rack Card
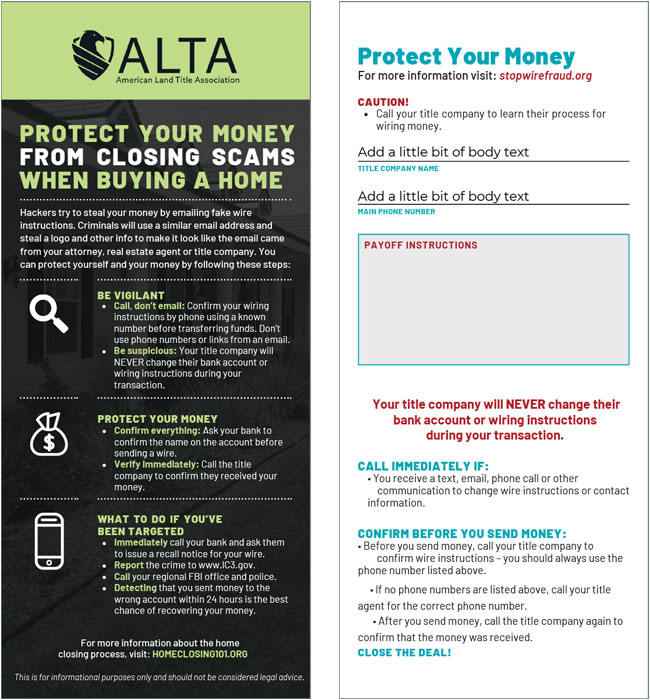 ALTA has produced this Rack Card explaining Wire Fraud. ALTA Members can brand the infographic with their own information at the ALTAprints website. This rack card can also be branded in 14 different languages.
ALTA has produced this Rack Card explaining Wire Fraud. ALTA Members can brand the infographic with their own information at the ALTAprints website. This rack card can also be branded in 14 different languages.
What is Phishing/Wire Fraud PowerPoint (Member-only content)
 Use this presentation to educate consumers about the dangers of phishing emails and wire transfer fraud. The presentation provides information on what to do if you’ve fallen victim to a scam and also highlights 10 tips to prevent wire fraud.
Use this presentation to educate consumers about the dangers of phishing emails and wire transfer fraud. The presentation provides information on what to do if you’ve fallen victim to a scam and also highlights 10 tips to prevent wire fraud.
Employee Training and Awareness
ALTA Insights Webinars
ALTA Webinars provide access to industry experts and the latest information about information security topics. Visit the Link to the ALTA Insights Webinars to learn more.
Monitor and Improve Employee Skills
Consider a phishing security test for all of your employees. These companies can help:
- Security Planner: https://securityplanner.org
- PhishMe: https://phishme.com/free
- KnowBe4: https://www.knowbe4.com/resources
Information Security Articles
Recent 2025 2024 2023 2022 2021 2020 2019 2018 2017 2016 2015 2014